Welcome to the “Authorize” clipping service, a precursor to an upcoming authorization-themed conference. This service is provided by volunteer authorization nerds who want more people to know about all the cool stuff that’s going on in the authorization world!
😲 News and announcements
Match of titans: This news is so big, involving such gigantic companies, that we’ve gotta cover it first. You might even just have heard about it already: Google is in advanced talks to buy Wiz for $23B, its largest acquisition ever. Over at CSOonline, Ray Wang suggests two advantages of the pairing: “One, cloud security is hot and allows Google to cut into AWS and Azure clients, and two, having Wiz would give them some consistently large workloads to monetize.” Yep and yep.
Big moves: Our own Sarah Cecchetti, who brought the Cedar language to market at AWS (along with co-founding this humble newsletter, IDPro, and many other achievements), is joining Beyond Identity as their Head of Product. Hearty congratulations from your AuthZ nerd friends!
Secretive security: Startup Sola Security, headed up by former Cider head Guy Flechter, has landed a $28M seed round. Per Calcalis Tech, “Sola does not yet have a product, only a direction for the development of a new cyber technology that has yet to be revealed.” 🤷🏻♀️
Getting organized: Github has rolled out an Organization-level role to grant permissions that apply to all of of an org’s repositories, along with five handy predefined roles for collections of permissions.
🤓 Explications and explorations
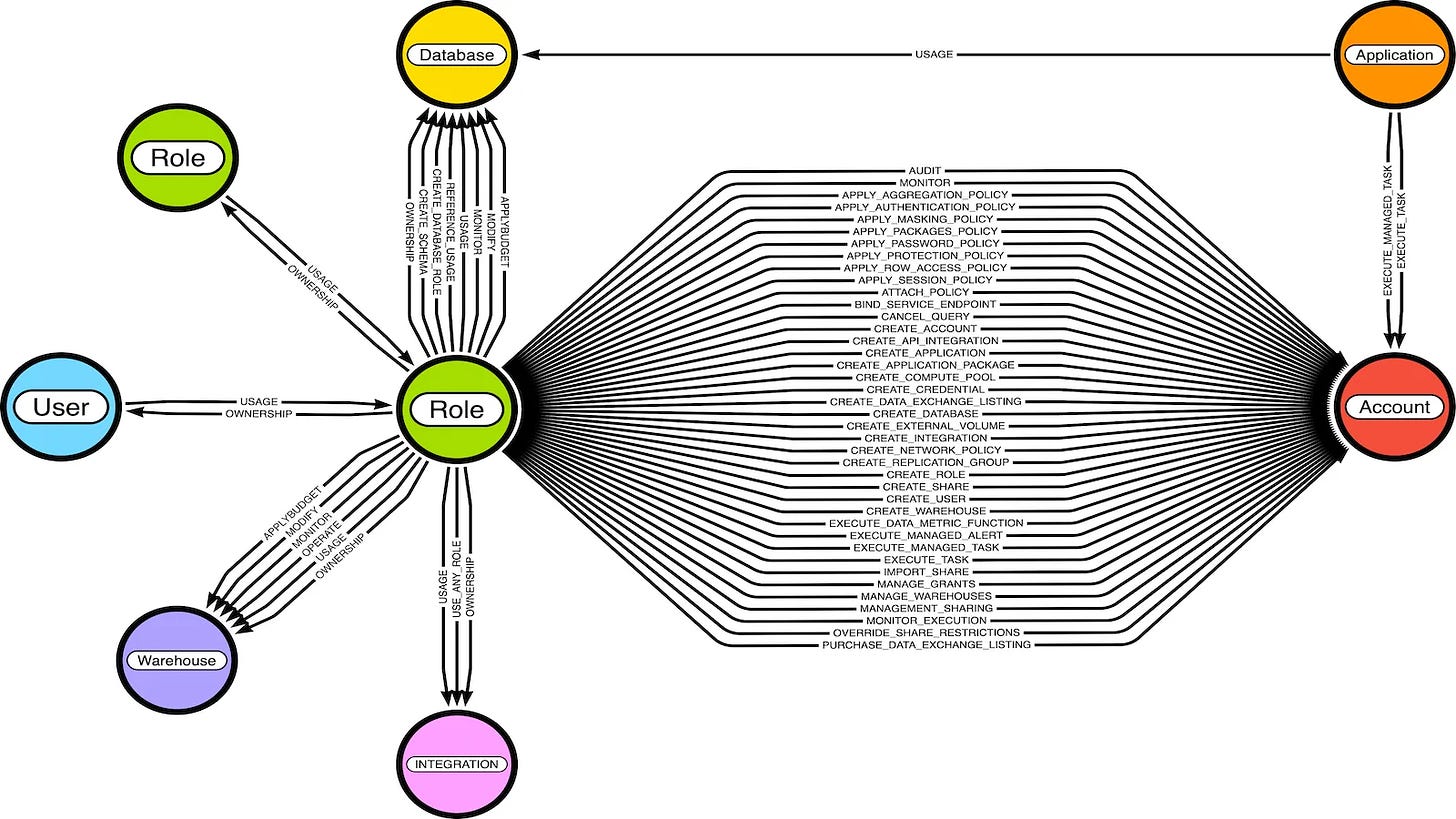
Mapping special snowflakes: Jared Atkinson of SpecterOps does the world a favor and maps Snowflake’s access landscape in detail. This points to how complex authorization can become in the context of a hosted database, which has policies at the cloud, network, table, and service levels.
Ask yourself, “Can you answer which users can use the
DATASCIENCEDatabase in your Snowflake deployment?” With this graph, that question is trivial to answer, but without one, we find that most organizations cannot answer these questions accurately.”
Shell game: Oracle Cloud Shell has a new feature, offering more control over public network access. It’s all about battling unauthorized access through a combo of network, security zone, and IAM policies.
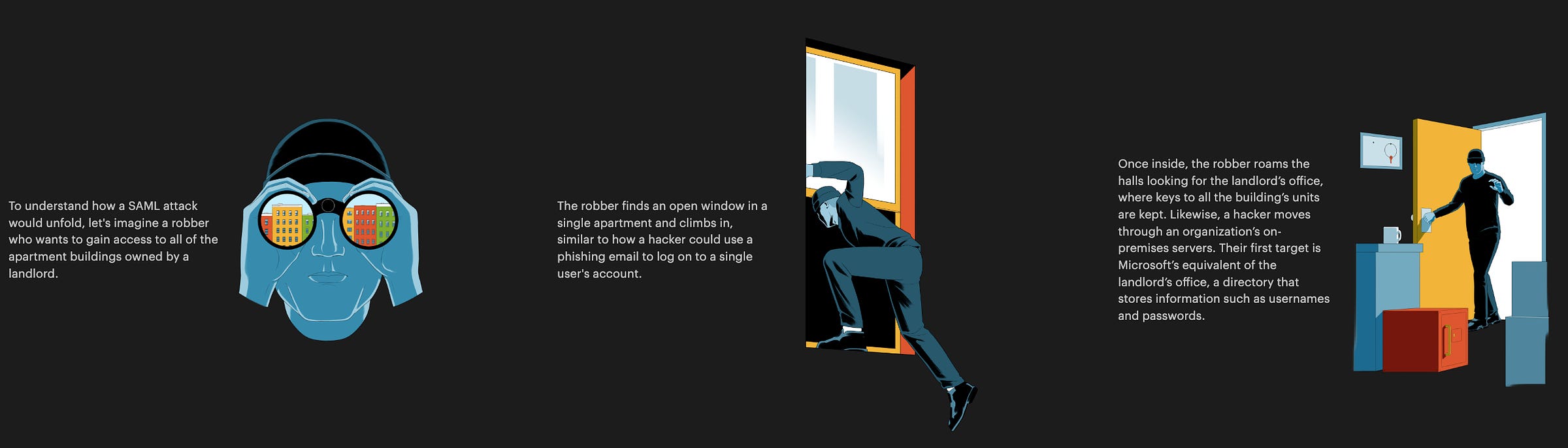
Longread: A whistleblower from Microsoft's IAM security team alleges that long-standing weaknesses in Active Directory Federation created unauthorized access risks that were later exploited in the SolarWinds attack. ProPublica helpfully illustrates how the so-called (and not much loved by the IDPro community) “Golden SAML” attack works. An excerpt…
If you’re an authorization nerd and an IDPro member, join our discussions in the IDPro Slack #authorization channel! Want to help write this newsletter and organize authorization conference activities? Find Rohit Khare on LinkedIn and ask for an invite.