IETF is coming to town 🌄
IETF 120 is in full swing in Vancouver and the AuthZ nerds are lurking in the hallways
It’s nearly midnight on Sunday evening here in sunny Vancouver (well clearly not right this minute) and it’s been quite a day. Brunch with friends, a hike, and eventually my first ever participation at IETF. And to round it off, my AuthZ partner in crime, Jeff Lombardo of AWS, and I cheered to OAuth, AuthZEN, Cedar, and ALFA from the rooftop of Vancouver’s Convention Center.
And speaking of IETF, stay tuned for more information regarding an impromptu authorization event (see below).
In & Around Authorization 🎯
Identity behemoth Okta is launching a competition to promote innovation. The Okta SaaS Startup Competition will allow early-stage startups a chance to receive a cash investment and support from Okta.
Forbes released an interesting article on a nascent topic, the digital twin.
A digital twin is a virtual replica of a physical system or asset, which enables simulation and modeling of real-world processes. Because the digital twin is informed by real-world data, it can be used to generate valuable insights and drive better decision making.
Read on here to understand how that impacts Identity & Access Management.
Notion, A new tool that blends your everyday work apps into one. is the all-in-one workspace for you and your team (in their own words). It’s no surprise then that authorization is a big challenge for them. Zach Smith peeled back the covers on how they do it in this YNews post.
RAG is also a hot topic in the news lately. Retrieval-augmented generation (RAG) is a technique for enhancing the accuracy and reliability of generative AI models with facts fetched from external sources.
Vectara Secures $25 Million Series A Funding to Advance the Trustworthiness of Retrieval Augmented Generation with New Mockingbird LLM. And Vectara is not the only believer in RAG. Check out this interview of Databricks co-founder and CEO Ali Ghodsi.
Authorization ABCs 🔤
If you want to learn more or you just want to brush up on your skillset, here are a few useful resources.
Toxic Role Combinations are dangerous: these risky configurations pose significant threats, from unauthorized access to fraud, creating fertile ground for internal vulnerabilities. Without vigilant oversight, the repercussions for organizations can be significant, including financial loss, reputational harm, and regulatory penalties. Learn more here.
Access Governance: organizations need to perform regular user access reviews on applications in scope to determine who still has access, verify that they need continued access, and remove access from anyone who doesn’t. Learn more here.
Product Updates 📦
Google Distributed Cloud air-gapped appliance is generally available: this is interesting as it’s somewhat a reversal of everything ☁️. And it comes with security at its core:
Google Distributed Cloud air-gapped appliance is designed to operate without any connectivity to Google Cloud or the public internet. The appliance remains fully functional in disconnected environments, preserving the security and isolation of the infrastructure, services, and the APIs that it manages. This makes it ideal for processing sensitive data, while meeting strict regulatory, compliance, and sovereignty requirements.
The Big and Mighty are not the only ones with new releases. Cerbos, the AuthZ startup, has just announced its authorization hub is officially GA.
API Security 🛜
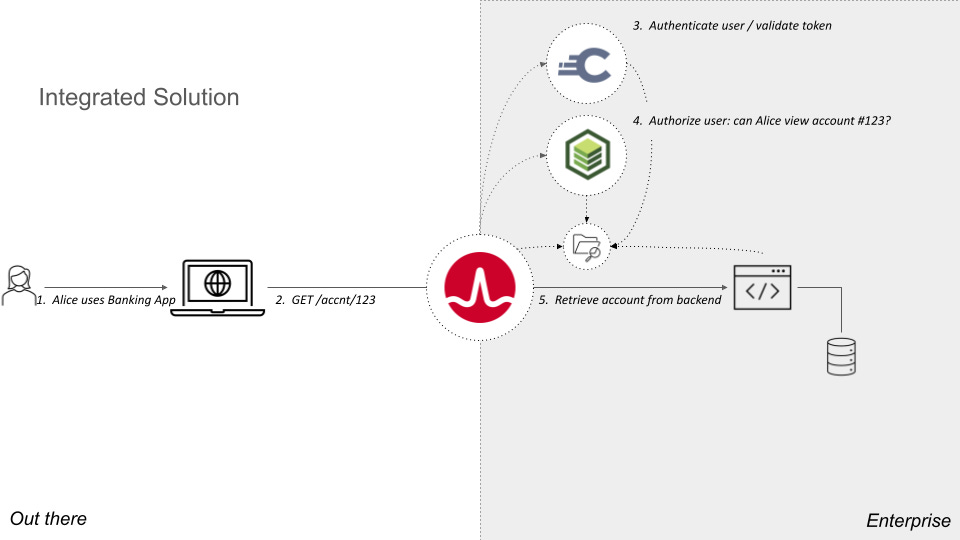
Last month, at Identiverse, API security was top of mind. Many referred to the OWASP Top 10 API Security Risks and most notably API1:2023 - Broken Object Level Authorization. This week, we’re happy to bring you three articles that delve on authorization applied to APIs:
My peer, Omri Gazitt of Aserto wrote a great two-part piece on API Authorization:
I was fortunate enough to be included in Nordic APIs newsletter with an article on building API authorization from scratch.
IETF Bulletin 🔧📰
If you’re in Vancouver, there are several topics worth checking out in terms of authorization:
The OAuth Working Group will have 3 sessions:
Monday from 1pm to 3pm PT
Tuesday from 3:30pm to 5pm PT
Friday from 1pm to 3pm PT
The WIMSE Working Group will have 1 session:
Wednesday from 9:30am to 11:30am
Additionally, I will be presenting ALFA 2.0 both in OAuth’s Friday session and in a dedicated side meeting on Thursday at 2pm in “Tennyson”.
Details are in the IETF 120 Agenda.
Several AuthN/AuthZ nerds will be lurking in the hallways so come chat with us.
To wrap it up
For those of you in Vancouver this week, come meet us on Tuesday night during the Board Game event. Jeff brought his notorious Alien 👽Cedar-based Permissions Game. Will you escape unscathed? Only one way to find out.



