Codified Raises $4M seed round
And more news from the access management world
Welcome to the “Authorize” clipping service, a precursor to an upcoming “Authorize” conference. This service is provided by volunteer authorization nerds who want more people to know about all the cool stuff that’s going on in the authorization world! Here’s all the news you need to know.
Events
Seat reservations are now open for RSA Conference. Reserve your seat today for Permissions: Centralized or Decentralized? Both!
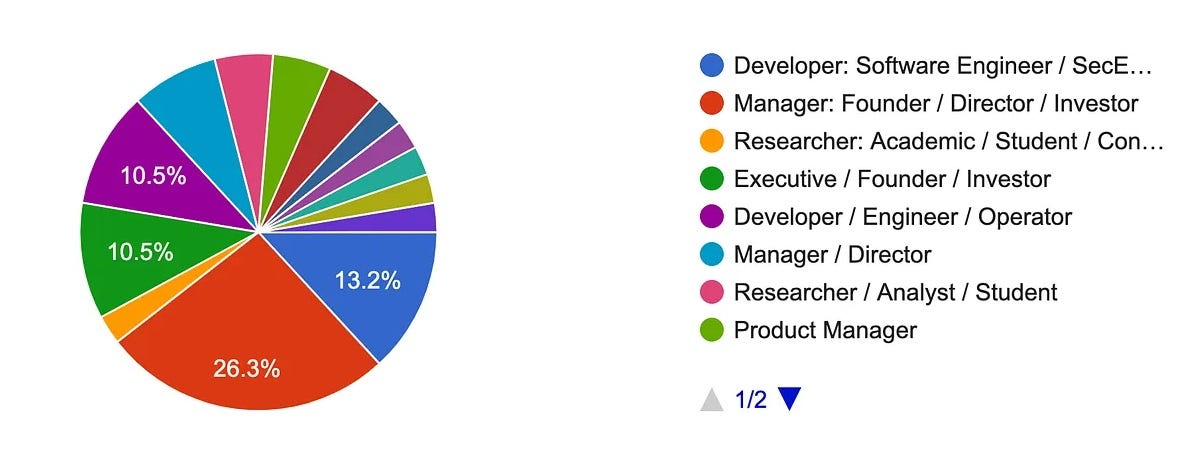
We’re starting a conference this fall focused entirely on access management. Please let us know what you want to see. Here are some initial results of who is interested in coming:
The next Internet Identity Workshop is just six weeks away. If you’re coming, please announce your interests in our virtual blackboard for An Unauthorized Unconference at IIW [April 2024].
People are constantly building cool new stuff
Check out version 0.31 of the Topaz OSS authorizer, now with support for a full complement of ReBAC operators: union, intersection, exclusion, and relation navigation (arrow operator)! It also comes with a set of templates based on the fine-grained authorization systems used for Google Drive, Slack, and GitHub. Read the announcement post, or clone the repo.
Mergers, Acquisitions, Investment and Partnerships
Google Cloud adopts some pet startups: GCP chose 17 startups using AI to change the future of cybersecurity, including some AuthZ adjacent winners:
Cakewalk “Access Management, made neat” that’s “design-first” and originally aimed at SMBs
Gomboc.ai “automatically fixes cloud security problems while making sure everything still works correctly, including any security policy violations” using “plain text policies” to correct infrastructure-as-code (IaC) templates.
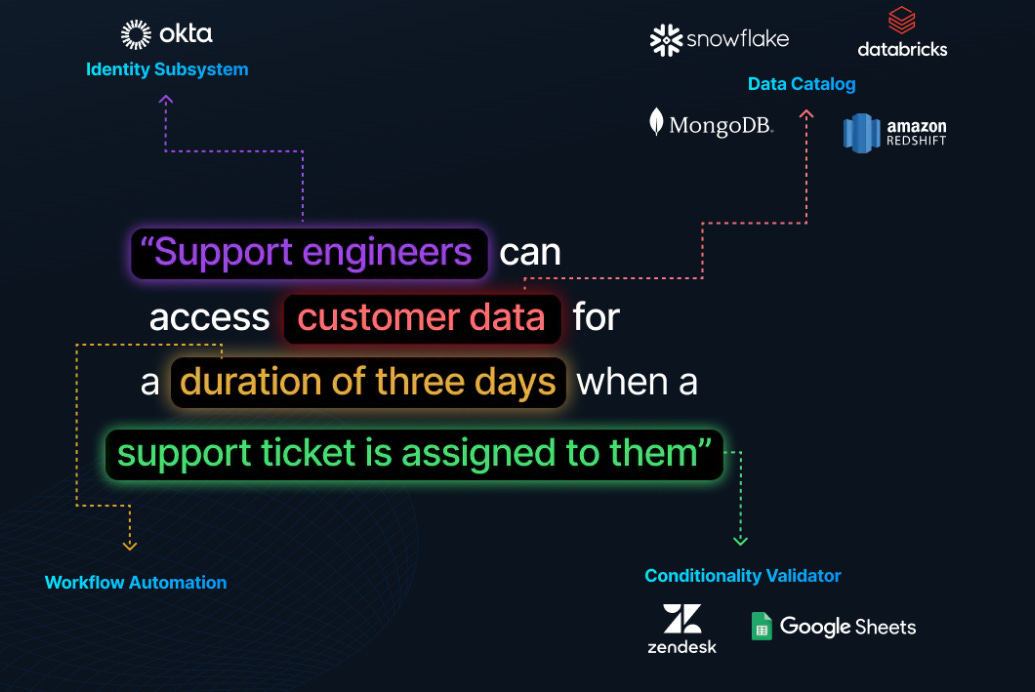
Madrona Venture Labs incubated the Seattle-based startup Codified to power “policies that you can write in English,” and it just announced a $4M seed round. Former Snowflake and Microsoft execs back new data governance startup
Standards
Let’s all do the NIST again: After years of consultation, the CSF added a sixth domain all AuthZ adepts are adamant about: Governance. To learn more about the “identify, protect, detect, respond, recover and govern” sextet, start from NIST Cybersecurity Framework 2.0 Officially Released
News
Least Privilege, Most Effective: According to the IBM X-Force 2024 Threat Intelligence Index, what’s old is still news: “84% of attacks on critical sectors, compromise could have been mitigated with patching, MFA, or least-privilege principles” Or, as they emphasized in a video, “It’s a lot easier to log in than hack in.” The old, not the new: Basic security issues still biggest threat to enterprises
Gone in 60 127 seconds? CrowdStrike’s 2024 Global Threat Report claims they detected a complete Cloud breach completed within 2’07”, with the average falling to an hour [Blog]. The authorization angle is that attackers can resemble ordinary, over-privileged users who just happen to start using some more privileges than they ought to have.
Licenses are permissions, too: Thor’s hammer of shutting down a maximum severity incident where an app designed for remote access is thoroughly subverted? Just treat your customers like copyright pirates and yank their license keys. After all, your AuthZ can’t fail if it can’t be executed, right? ConnectWise ScreenConnect Mass Exploitation Delivers Ransomware
Compromised AWS Account IDs Here’s how an AWS IAM policy language hack for detecting the ownership of any public S3 bucket was recently extended to even private S3 buckets, by combining VPC Endpoints with CloudWatch logging: How to find the AWS Account ID of any S3 Bucket Like a film noir safecracker, digit-by-digit an attacker can dial in an account number using wildcard rules on resource permissions…
Gen AI is a new threat to cyber security. Here are ways do defend against it (Number two is zero standing access!)
If you’re an authorization nerd and an IDPro member, join our discussions in the IDPro Slack #authorization channel! Want to help write this newsletter and organize the conference? Find Sarah Cecchetti on LinkedIn and ask for an invite.