Read on for our next Happy Hour, our new submission system, and two new AuthZ tools!
Nope, not a movie reference this week. Not even when this issue’s awesome cover art is from America’s 220th birthday blockbuster. Also notwithstanding the obvious AuthZ twist at its climax, when “an alien invasion is averted by a computer virus cooked up by Jeff Goldblum.” No, it’s simply because it’s that time of year when the people’s thirst for publishing all the links authorized to click simply cannot be slaked with the parched pace of product announcements held back for a holiday!
New Submission Form
“When in the course of authorized events, it pricks the conscience of the editors to ease their pursuit of publications by beseeching every subscriber to send in their own Submissions…”
Yep, a slow news week is why it’s time to turn to a new Google Form, to encourage all 700+ of our dear readers, to send in your own leads for Events, Articles, Media, and Software (or Other) clippings about Authorization, ranging from startups, software, and standards to new products, protocols, and policy languages.
New Events
Without new events this week, we made up our own… Save the date for the Third AuthZ Subscriber Social at IETF Vancouver on Tuesday, July 23. It’s co-located with the official IETF Board Game Night, in hopes of coaxing the creators of Aliens vs. Permissions to challenge all the AuthZEN adepts and WIMSE wizards to escape their tentacled clutches as described two issues ago.
If you want to help schedule, sponsor, speak, or just snipe, just join the authorize@ mailing list for an invitation to call into the fortnightly tomfoolery.
New Media
There were several sparklers streaming in since last week:
IDPro’s interview of identity professional Omri Gazitt, co-founder and CEO of Aserto
Zuplo & OpenFGA’s webinar on Mastering Fine-grained Authorization
…and a panel with Permit.io, 3Edges, and Axiomatics, provocatively premised ABAC vs. ReBAC: An Authorization Policy Showdown



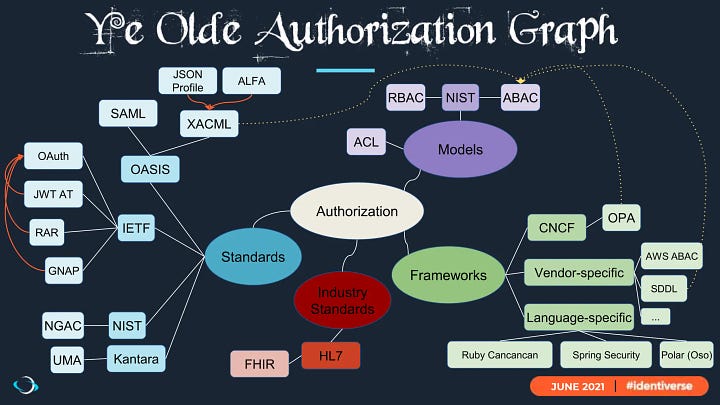
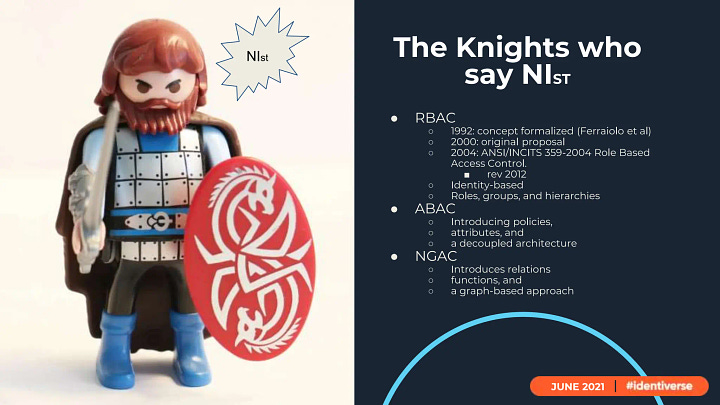
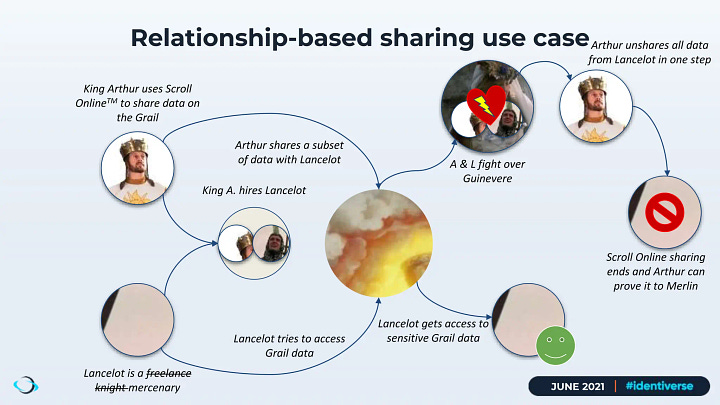
Let’s slip in a superlative survey from a few months ago that’s still worth a watch —if only to see one of our esteemed editors of UMA portraying an Uma — in The Holy Grail of IAM: Getting to Grips with Authorization. This talk was remastered on Apr 9, 2024 based on a presentation at Identiverse from 2021 that romps through an entire AuthZ landscape as absurd as anything accomplished by Monty Python, yet as trenchant at cutting through the crap as Kill Bill, Volumes I and II put together1

New Articles
Access AWS services programmatically using trusted identity propagation | AWS Security Blog on Jun 27, 2024 shows how single-sign-on can span the gaps from identity provider to cloud provider to service provider, all without the end-user ever acquiring an account of their own. The OpenID Connect (OIDC) application in the middle authorizes issuance of tokens that can call services as the user, rather than as a deputy on their behalf.2
Even if there were any more new articles, I’d still steer everyone towards studying the 2023 ACM System Software winner: Andrew Tanenbaum honored for pioneering MINIX, the OS hiding in a lot of computers | The Register
New Software
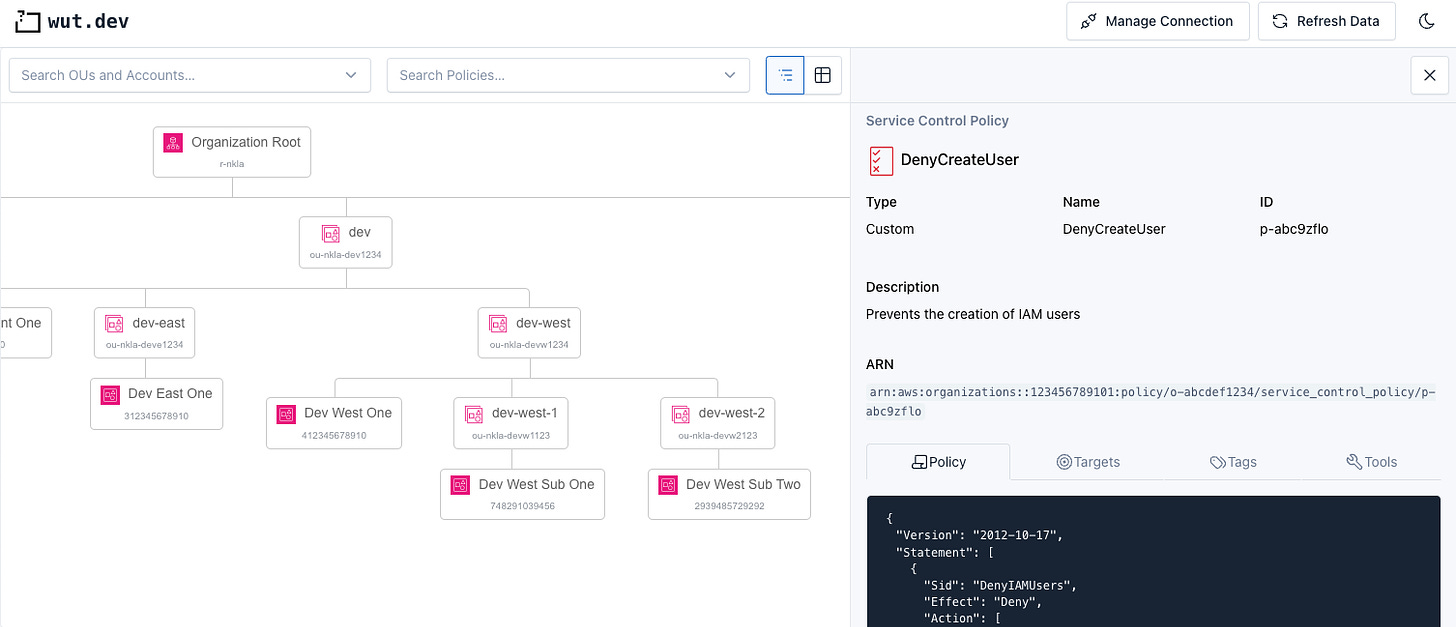
Introducing Wut.dev launched an entirely browser-based app to visualize and debug the dark arts of AWS Service Control Policies (SCPs), as they propagate up and down the hierarchy of accounts (with a tip’ o’ the hat to CloudSecList, “hand-curated by Marco Lancini”). A SCP-first tool is intriguing because they are difficult to test without simulators or analysis tools; risky to deploy, because it gets denies rather than warns; and can make errors more confusing to explain (since a developer may not be able to see the policy blocking their attempts). Not open-source, but docs are on GitHub.
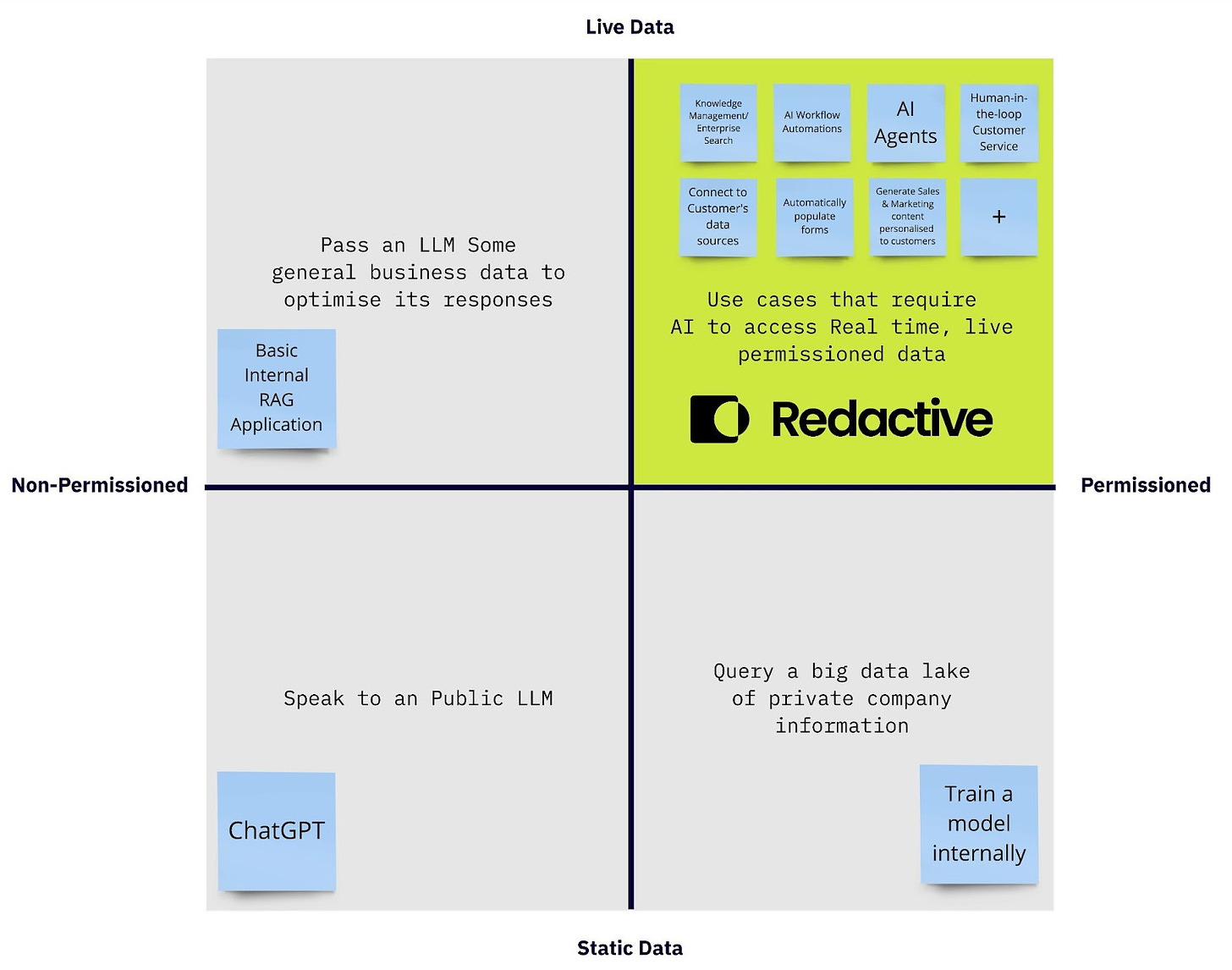
GPT.Redactive.ai “brings real-time, permissioned data access to ChatGPT,” while “maintaining strict data security through user-defined permissions,” according to an employee on HackerNews. Raising about $2M in September 2023 from the likes of Atlassian Ventures (former employers), this Australian startup blogged that “Trying to understand permissions is hard and doesn’t scale” in January 2024 and coined “Permission Aware Sharable Indexes” in March 2024. Any readers aware of any AuthZ tech they might be using under the hood?
Old Papers
Shot — some much older software: a pioneering Logic-Based Security Language from Microsoft Research called Binder, from 2002 and based on Datalog (with a tip’ o’ the hat to today’s CIAM Weekly for spotlighting it in Teleport’s History of AuthZ, itself from 2021). Long before Zanzibar or Cedar, John DeTreville posited a ReBAC-like approach that could recursively express policies about polices, such as “principal X can read resource R if X is a BigCo employee and X’s boss (Y) approves.”
Chaser — some much, much older hardware: Voyager 1 sends back science data from more than 15 billion miles away after NASA fix | CNN, a callback to my first byline.
Still shamelessly running up the cinematic citation count. Be very glad we only stole a phrase, instead of stealing the entire Declaration!
Or, if all my alliterative argot is erroneous in your expert eyes, simply submit your own corrected characterization! Our readers are surely smart enough to Attack the Confused Deputy in AWS IAM with even more abstruse (yet terrifyingly total) pwns that Implicit Self-Assuming Role Trust Policy almost permitted?