A few weeks ago, I decided to buy a new birdfeeder. The model I went for is a cute little contraption made of solid cedarwood. The one I got last year was no match for the many hungry squirrels that prowl about the trees in total disregard for property lines. Now, at least, the birdfeeder wouldn’t break. Yet, the squirrels would still be able to access the much coveted seeds. And I am no match for Mark Rober and his wonderful backyard maze. Knowing about authorization doesn’t mean you can actually build the physical system.
So I went for second-best: seeds squirrels wouldn’t like. A fortnight later, what’s the verdict? The birds don’t like the seeds either and I’m left with a birdfeeder still very much full to the brim.
Enough with the nutty anecdotes and on with the latest in AuthZLand…
Past Events 📅
Gartner IAM took place a few weeks ago in London. The opening keynote of this show “Treat Cybersecurity as Business Investment” reports Mark Cassetta, my colleague, and CPO at Axiomatics. Read his report here. Rezonate CEO Roy Akerman penned his own 10 Takeaways including:
“Identity Security Posture Management (ISPM) is coming into the spotlight”
“Conditional access with risk-based metrics is ideal”
“Self-correcting IGA and machine learning can really play a much bigger role now in offloading the overburdened IAM teams.”
Only 37% “Believe Your IAM Infrastructure Is Prepared to Be Resilient”
While business leaders were huddled in London, standards advocates were meeting at IETF 119, Brisbane. If you have a couple hours to spare, you can replay the entire Web Authorization session.
Of particular interest to our readers is the new profile that aims to apply Cedar to OAuth 2.0 Rich Authorization Requests:
WIMSE was also announced as a new working group. The increasing prevalence of cloud computing and micro service architectures has led to the rise of complex software functions being built and deployed as workloads, where a workload is defined as a running instance of software executing for a specific purpose. WIMSE will focus on the unique identity and access management aspects of workloads at runtime and their execution context, particularly focusing on the propagation, representation, and processing of workload identities. [more]
Upcoming Events 🔮
Identiverse has released its agenda and it’s packed with AuthZ topics, not least OpenID AuthZEN’s interop. If you want to take part, please contact the interop leads (Omri Gazitt and David Brossard) and check out our website. Of note as well:
Graph-Based Harmony: Simplifying ZTA in the Age of Data Breaches
Navigating the Intersection: IAM and OWASP in the Cybersecurity Landscape
With IETF 119 in the rearview mirror, it’s Vancouver’s turn to host IETF 120… Are you interested in an authorization-dedicated side event? Let us know here. 👍👎
Use Cases 📃
GitHub is where the world goes to code. Developers use it every day to manage their code repositories, projects, and issues. So maybe we should take a cue or two from them when it comes to access control. Aserto’s Omri Gazitt has us covered in his latest post, Authorize like GitHub! Learn how GitHub’s fine-grained authorization model works, and how to express it as a relationship-based (ReBAC) model.
Whoops 🫢
Up to 25% of Users Are Granted Access Beyond What is Required To Do Their Job according to CyberRisk Alliance [Mar 1, 2024] and excerpted in Identity security: Challenges and best practices as well as IAM survey reveals top implementation challenges on their SC Media site [Mar 14, 2024]. Based on a “survey of over 200 IT security professionals”:
After costs and cultural challenges, least-privilege remains a close 3rd place because “users do not understand the implications of allowing them to have more access than they need” (source)
“3 out of 4 respondents in the cybersecurity industry report being more concerned now about unauthorized access attempts than they were just 12 months ago.” (source)
The report is behind a loginwall here: Navigating the identity security minefield
Misconfigured Firebase instances leaked 19 million plaintext passwords
And what about the AT&T data breach? AT&T won’t say how its customers’ data spilled online according to a recent TechCrunch article.
New Investments 💰
BigID raises $60 million at over $1 billion valuation as it closes on $100 million in ARR. BigID, based in New York, produces software for data security, compliance, privacy, and governance.
Tis the Awards Season 🏆
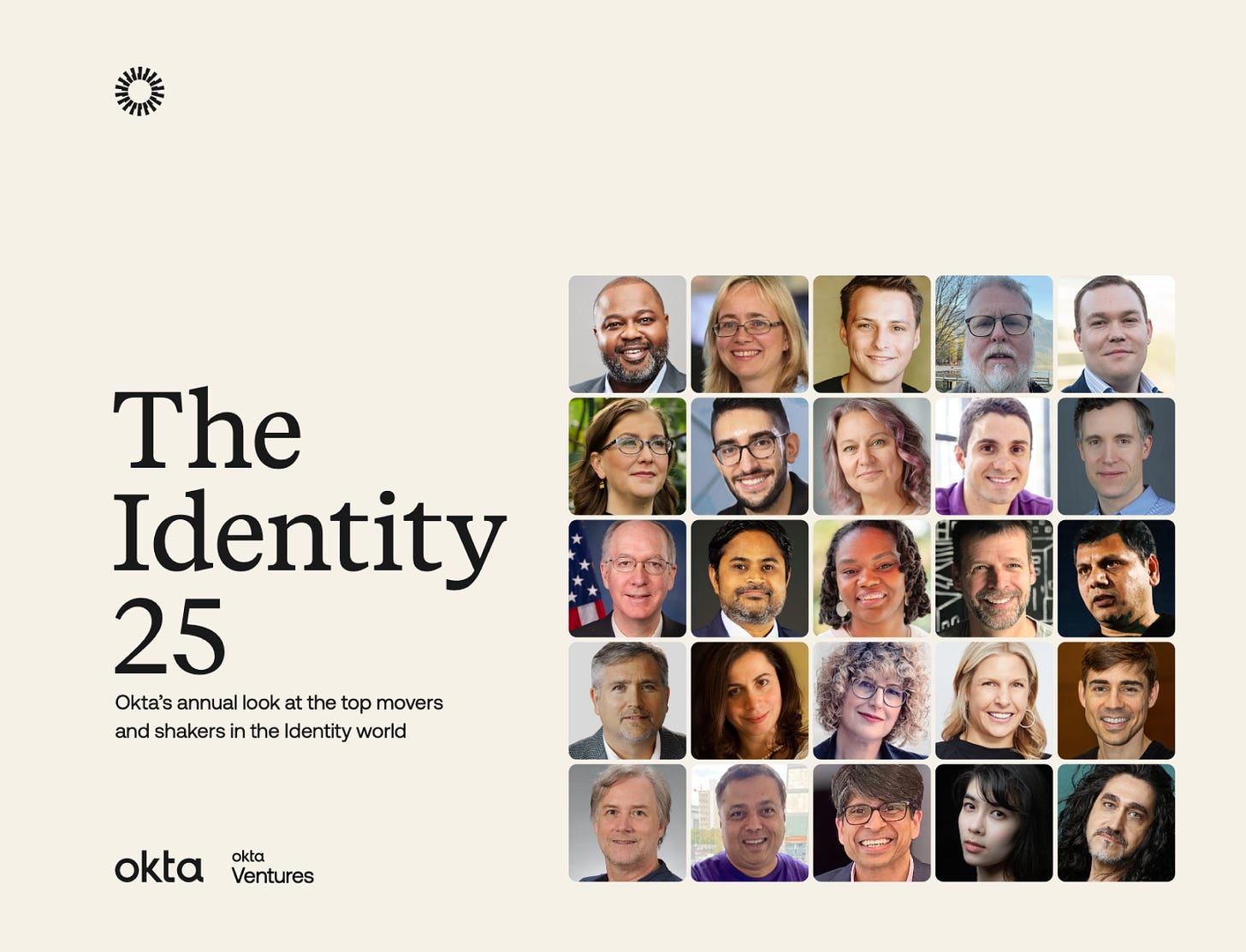
The Academy Awards have come and gone. Oppenheimer and Poor Things came out on top. In AuthZ land, we have our ceremonies. Okta, the IAM vendor, recently published a list of 25 influencers as part of Okta Ventures’ Identity 25 for 2024 including several names that have appeared on this newsletter such as
Dick Hardt, Hellō
Eve Maler, Venn Factory
Atul Tulshibagwale, SGNL
and last but not least my fellow curator Sarah Cecchetti.
Conclusion
Are you still watching Mark Rober’s epic video? Spoiler: the squirrels eventually break into Fort Knuts. Maybe it’s time to rethink the fort’s access control?
Happy Monday everyone!