The end of Summer (in the Northern Hemisphere) is celebrated on Labor Day (in the United States) with sighs of relaxation (from children), or regret (from children returning to school), or relief (from parents of children returning to school)!
It’s been a record-breaking peak flying season, so AuthZ hackers might be tempted to Bypass airport security via SQL injection | Ian Carroll to use Known Crew Member lanes (h/t to Jeff L on the IDPro #authorization Slack). Or bypass TSA lanes entirely, by flying private jets — which has its cyber analogue in Personal cybersecurity concierge is new perk, and need, among wealthy | CNBC!
Exhausted from all that “relaxation,” this issue is a tad tardy for Back to (Security) School season. That’s on you, dear readers: we depend on your submissions, which were, ahem, scarce this week. We still did some homework, though so now it’s time to buckle down and brush up to study us some AI… Authorization Intelligence, that is!
The least you need to learn…
Tratteria.io launched a new open-source Transaction Tokens Service based on IETF’s WIMSE proposals, in Secure Identity and Context in Microservices | SGNL
Exploring Fine-Grained Authorization with David Brossard | IDPro on Aug 28 (LI)
Context in Cedar Authorization Requests | Cedar Craft’s YouTube channel on Aug 28
Intro to the Cedarling | Gluu from Identerati on Sept 5 (slides, LI, wiki, docs, code)
A “new product at the Janssen Project” that can “run anywhere — as a local agent in the browser, embedded in a mobile application, or as a cloud service” and update instantly.
CommonFate 2.3 launched Cedar-powered IAMOps for Just-in-Time Access to S3
The more you could master…
Also from CommonFate: Cloud Access Management Maturity Model: Part 1 & Part 2
PaC that “ensures that the right people have access to them at the right time.”
And from WhiteSwan Security: Identity Security Maturity Model | Vinay Mamidi (LI)
“workflows that enable users and devices to request time-bound permissions”
Andromeda Security is also appearing alongside WhiteSwan at Identity Week’s Startup City on Sep 11-12 in Washington, DC Sep 11-12, 2024 for a pitch-off (LI)
AI to “Automate Permissions and Lifecycle for Human and Non-Human Identities”
Cerbos celebrated GA on a podcast Unveiling the Future of Authorization | Amazic Aug 30 & and blogging about PBAC vs. Zanzibar on Sep 4
AuthZEN: “open standards … promises greater interoperability and future-proofing”
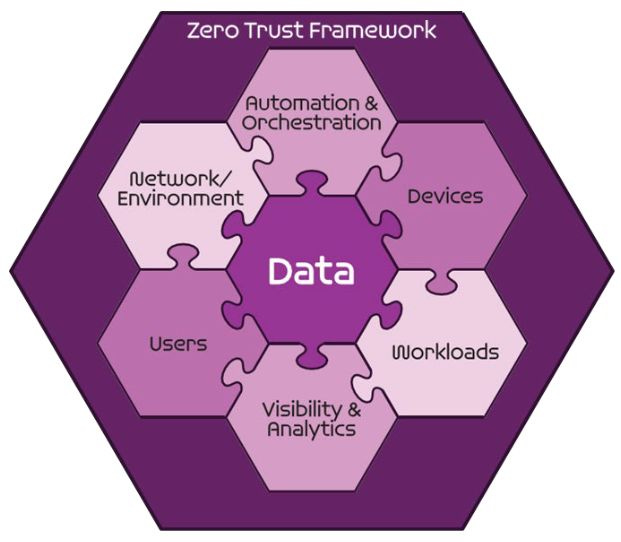
IDPro published a comparison of DoD & NSA’s Zero-Trust guidance to “educate as opposed to enumerate” — perhaps there’s a new Zero-Maturity Model to come?!) (LI)
…and always add an AI on top:
Leveraging AI for Effective Authorization | IC-Consult.com (LI) Webinar coming up Sep 24 with David Brossard about “how artificial intelligence can simplify policy complexity, prevent administrative bottlenecks, and assist in creating effective authorization policies.”
Migrating to an Identity Centric Authorization Strategy | The Cyber Hut & PlainID on Sep 12 hints at Generative AI’s potential to “create human readable and adaptive access control policy” with Simon Moffatt & Mickey Martin, respectively
Win the Race Against AI-Driven Fraud | Ping Sep 17, 2024 with Eve Maler (Venn Factory) and Kevin Lee (Sift) — because black hats also have access to AI!
DevSecCon: Developing AI Trust | Snyk Oct 8, 2024-Oct 10, 2024, Virtual, CFP
Looking forward to talks from Daniel Miessler (Unsupervised Learning) and Open Source Oopsies! from John Hammond (Huntress)
Unlocking the Power of AI in IAM | David Lee (Identity Jedi) in his latest issue laid out a vision for “where AI really starts to earn its keep in IAM: understanding access privileges” — but there may be entirely new entrants who win out. Why? “AI and Data Mining have to be at the core of what they do, not just an add-on.”
How Generative AI Elevates Situational Awareness in Cybersecurity | Balbix at a virtual Google Developer Group (GDG) on Aug 28, 2024, Aravind Iyengar spoke about “the hard ROI of cybersecurity AI assistants” like their BIX virtual analyst (video, slides)
Upcoming seminars & symposia
Early-bird registration ends Sept 9 for Authenticate 2024 | FIDO Alliance on Oct 14-16 in Carlsbad, CA, including IAM talks and AuthZEN: Standards for Modern Authorization
The Authorization Clipping Service was proposed one year ago at the Internet Identity Workshop, and the 39th edition is coming up on Oct 29-31 in Mountain View, CA
Right after Halloween will come Dia De Los Hackers | Pacific Hackers Conference 2024 on Nov 2 at Hacker Dojo in Silicon Valley, with a CFP open until Sept 29
CNCF Cloud Native StartupFest on Nov 12 in Salt Lake City, UT hosts The $100B Opportunity for the Cloud-Native Ecosystem, a VC panel so diverse it ranges from Google Ventures, to an ex-Googler’s fund, and a Xoogler (Natalie Vais, Spark Capital). Another Xoogler in the news is privacy pioneer Lea Kissner, LinkedIn’s new CISO!
An Uncaught Exception…
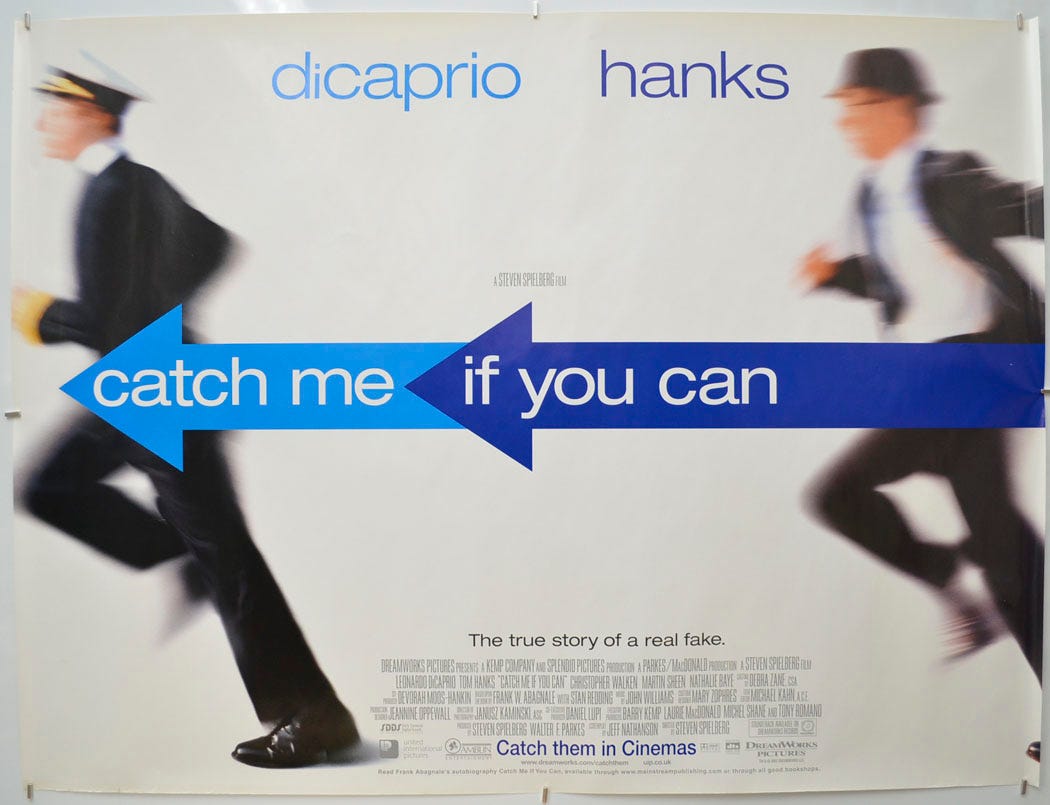
Alan C. Logan published The Greatest Hoax on Earth: Catching Truth While We Can in 2020. The tall tales Frank told on a game show in 1977 were already debunked in newspapers by 1978. Unfazed by facts, he persisted and published his fictional “autobiography” in 1980, which was distorted yet again on screen in 2002 (and stage in 2011). Yet even long after the truth came out, Frank was still conning universities into paying his speaker fees in 2021! (“to speak about Cybercrime and not about his life”)

I couldn’t tell you what the lesson to be learned is, but it might be that our identity isn’t our own — it’s what others believe it to be. I’d rather trust fellow citizens over corporations, which is why I’d prefer to phollow Phil Windley’s Digital Identity and Access Control (Aug 28):
“Until we value freedom and independence in the digital world, we will yield up control of our digital lives to others who will act in their own interests, not ours.”